CRIO Tips: Setting up VNC
This a follow on article to a couple previous articles: here and here. Its part of a series of tips that Neil Crossan provided me with, dealing with cRIOs and Linux RT targets. He saw a post of mine and sent me a bunch of tips and tricks. I thought I would share some of them with you here. Many thanks to Neil for sharing his knowledge. Also, general Linux knowledge is really helpful. If you want to brush up, here is a good book.
The Challenge
With an embedded UI, now you can have a touch screen connected to your cRIO and you can have a nice interface. However, what if you want to access that interface remotely? The easy thing to do is to use VNC. It’s more or less the equivalent of Microsoft’s Remote Desktop, except it is cross platform. It works very well in development. It can be very useful if the cRIO is on the other side of the lab and you want to interact with it without walking all the way over there. As you’ll see when we get to the security section, I’d be leery of using in production, unless you pass it through an encrypted tunnel.
Setup
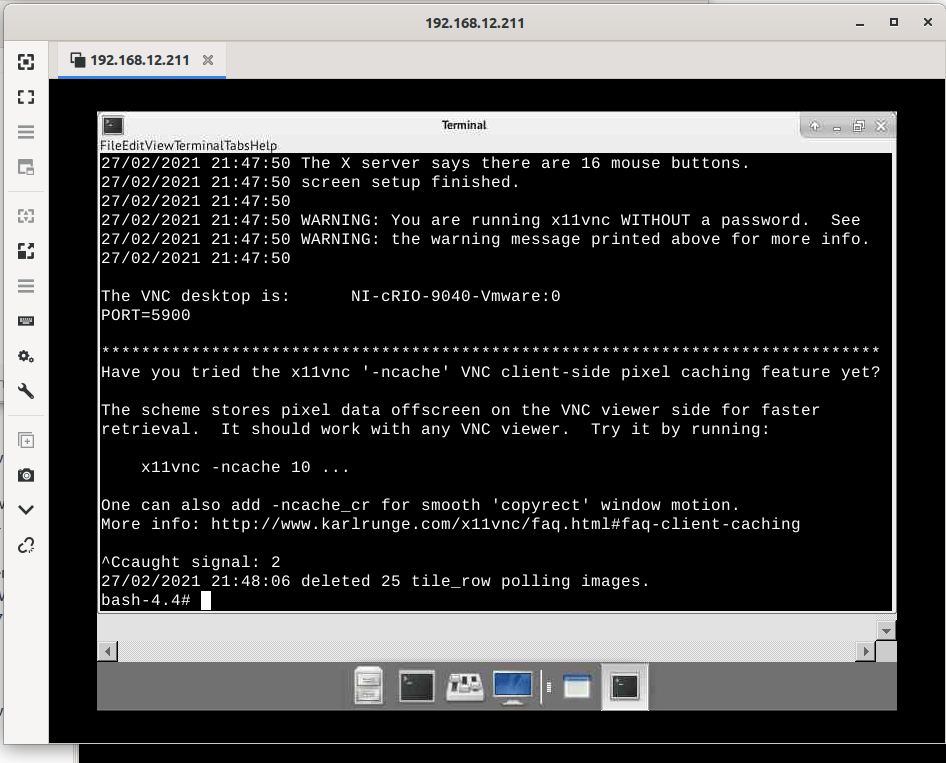
First we need to install x11 vnc.
opkg update
opkg install x11vnc
#if you are on an actual terminal on the embedded UI
x11vnc
#if you are logged in via ssh, set the display first
DISPLAY=:0 x11vnc
That will install and start the VNC server. Now you can connect through a VNC client. There are a variety out there, just use google and find one you like. Type in the IP address of your cRIO and it should connect.
Security
If you thought it seemed insecure that you could simply connect without anything more than the IP address, that’s good. That means you are paying attention. It is terribly insecure. So let’s make it a little more secure.
As lvuser, type in x11vnc -storepasswd You’ll be asked to enter a password and verify it. It’ll also ask you to store it to a file. Do that. Now when you run x11vnc if you type in x11vnc -usepw it will require the password. If you type in x11vnc without -usepw then it is still wide open.
All that being said, the connection is still not encrypted. If you are in the lab on the same local subnet, probably not too big a deal. Dut definitely keep the traffic within your own network and certainly don’t expose it to the internet. If you need to access the cRIO remotely, connect into the network via a VPN and then all the traffic stays inside the VPN. Also due to the lack of encryption you probably should be weary of leaving it on in production.
Starting VNC on boot
Before when we typed in x11vnc, it started the server running, but as soon as that process dies the server dies. If you reboot the machine, it won’t be running. If you are using it just for debugging in the lab, that may be fine.
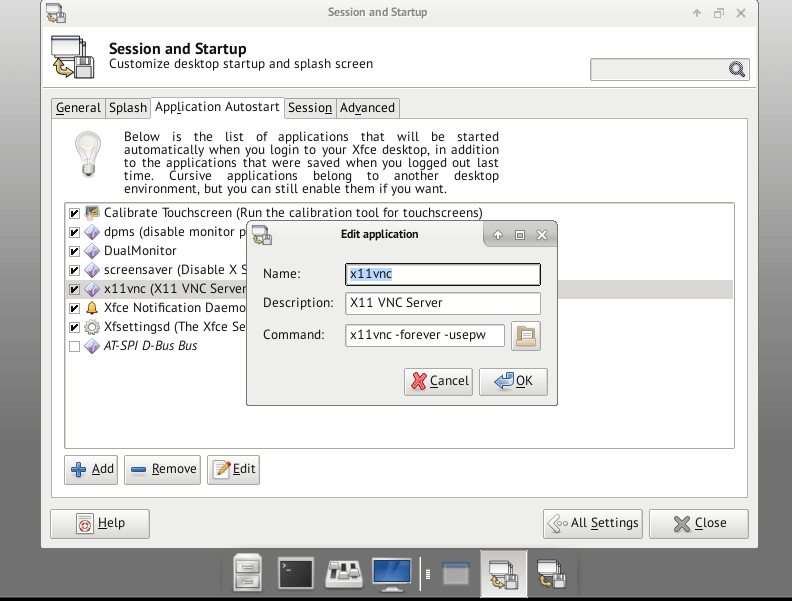
However if you use vnc a lot, you probably don’t want to have to start up the vnc server all the time. In that case, you can set it up as a startup program. Go to Settings and then to Session and Startup. Click on the Application Autostart tab. Click add. Then enter the commands as seen in the image below. We add the -usepw flag and a -forever flag. Forever is needed because by default the server closes when the client disconnects. Forever causes it to continue to run so you can disconnect and reconnect. Then just reboot the cRIO and you should be good to go.
Here is a forum post with more information:
https://forums.ni.com/t5/NI-Linux-Real-Time-Discussions/Installing-and-using-x11vnc-on-a-2016-x64-target-remote-UI/m-p/3471336?profile.language=en
Help!
If you would like help setting up a CRIO system and using Linux RT, give us a call. We’d be glad to talk about how we can help.